Cryptographic Risk Management in the Post-Quantum Era
Cryptography, a Foundational Pillar of IT/OT Cybersecurity
Cryptography is the foundation of cybersecurity. It secures communications and protects critical data at the heart of IT/OT systems. But cryptography can become a vulnerability when it is poorly managed and left outdated, or even if certain data flows are left unencrypted. When it fails, the entire structure of digital trust begins to crumble: signatures lose their validity, confidential data is exposed in plain text and identity theft becomes possible. Long confined to the background, cryptography is now emerging as a central issue in the age of the quantum threat—one that demands immediate and strategic oversight.

Discovery: Understanding Your Cryptographic Assets for Better Management
You cannot secure what you cannot see. Identifying cryptographic assets is the essential first step to regaining control of your security, revealing the true scope of cryptography use that is often underestimated and poorly documented.
The next step is the inventory process that organizes this knowledge into a clear mapping—algorithms, keys, certificates, protocols—and consolidates it all in one place.
Finally, auditing ensures ongoing compliance and resilience. It identifies vulnerabilities and deviations, providing guidance for continuous improvement. Together, these three pillars establish the foundation for a coherent, managed, and crypto-agile cryptographic policy.
The Quantum Computer Challenges Modern Cryptography
The security of traditional cryptography is based on the computational difficulty of solving certain mathematical problems with today’s processing capabilities. However, the transformative technology behind quantum computing, coupled with rapid algorithmic advancements, is redefining the landscape. Asymmetric cryptographic systems like RSA and ECC—widely used today—will become vulnerable with the advent of the first Cryptographically Relevant Quantum Computers (CRQCs). This won’t just weaken security; it will lead to a complete collapse. We are, therefore, on the verge of a true cryptographic revolution.
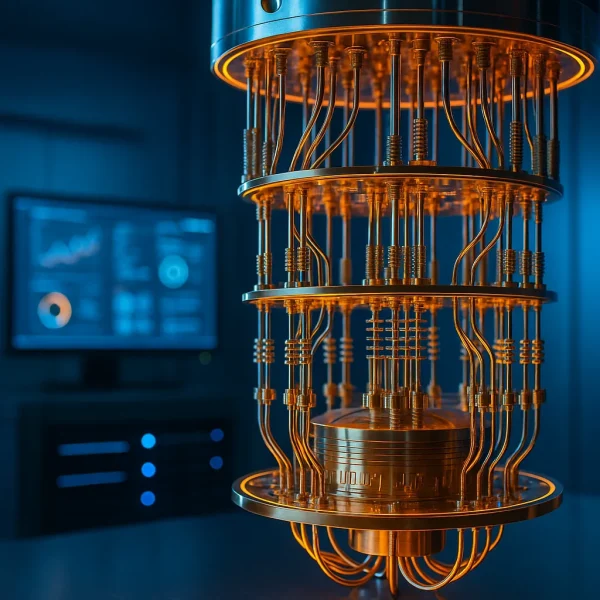
The Countdown Has Begun
The acceleration of advancements in quantum computer development, combined with recent optimizations of Shor’s algorithm, has prompted national security agencies to advance their roadmaps for migration to post-quantum cryptography (PQC):
- The UK’s NCSC, for example, recommends that organizations complete their cryptographic discovery and inventory phase by 2028 and migrate their most sensitive systems by 2031
- France’s ANSSI advises organizations handling data with a projected value in 2030 to implement a transition strategy immediately
- Australia’s ASD mandates the ban of traditional cryptographic algorithms starting in 2030
- The US’s NIST has announced the deprecation of traditional algorithms by 2030, followed by their complete prohibition effective 2035
Beyond these deadlines, the threat is immediate for sensitive data with long lifespans (over 10 years), as malicious actors are already collecting and storing vast quantities of data exchanged over the internet, aiming to decrypt it once quantum computers become capable. This scenario is known as “Harvest Now, Decrypt Later.”

In the Face of the Quantum Threat, PQC is the Answer
Post-quantum cryptography (PQC) is currently the only practical solution recommended by cybersecurity agencies to counter the threats posed by quantum computers. It is based on mathematical problems that, according to the latest scientific knowledge, remain secure against both traditional and quantum attacks, and introduces new methods for digital signatures and key exchange.
In 2024, the U.S. National Institute of Standards and Technology (NIST) finalized guidelines for three algorithms—ML-KEM, ML-DSA, and SLH-DSA—after an extensive international review process involving researchers and industry experts since 2016. CryptoNext Security played an active role in this effort. Although not selected by NIST, the FrodoKEM algorithm was adopted by the European Union as a complementary standard. These initial algorithms provide a strong foundation for building a quantum-resistant cybersecurity strategy.
Post-quantum cryptography (PQC) is fully developed and prepared for broad deployment, whereas Quantum Key Distribution (QKD) remains experimental and challenging to scale commercially.

Remediation: Ensuring Long-Term Security
After the asset inventory comes remediation, the only way of ensuring that your data and communications are truly protected against quantum attacks.
Depending on the system in question—be it a signing application, a hardware device such as an HSM or a secure communication server—the remediation strategy will vary. It may involve implementing a hybrid approach, replacing vulnerable traditional algorithms with PQC or adapting communication protocols to support the new technology. In IT, OT, and IoT environments, this requires a tailored strategy that fits each system’s constraints.
This phase is critical. If poorly executed, it can introduce new vulnerabilities. That is why it is essential to rely on robust tools, such as crypto libraries, providers, proxies, and hardware from trusted, specialized vendors. Remediation is also a strategic opportunity to adopt a crypto-agile approach and avoid facing this kind of overhaul again in the future.
Towards Agile and Controlled Cryptography for Resilient Cybersecurity
In this new era of cryptographic disruption—where emerging algorithms will address evolving needs while others become compromised—cryptography management is becoming a critical enterprise skill. Organizations must now manage their cryptographic assets just like any other component of information system security: updating, replacing or adjusting them in response to vulnerabilities or regulatory changes. The leading practice for achieving this is crypto-agility, the ability to add, modify or remove algorithms without causing significant disruption to system architecture.
As organizations shift toward post-quantum cryptography, implementing a crypto-agile framework with the right tools and resources is no longer optional. It is a strategic opportunity to ensure long-term security and resilience.