See what’s hidden: Take stock of your cryptography
The challenges
Cryptography: your biggest cybersecurity blind spot
Cryptography is everywhere. It is scattered throughout an organization’s applications, infrastructure, protocols, and network traffic, but is rarely inventoried or properly documented.
This lack of visibility exposes organizations to unmanaged risks, compliance issues, and an inability to effectively transition to post-quantum cryptography.
Hidden Vulnerabilities
“ We don’t know exactly where cryptography is being used, and we may already be at risk without realizing it.”
Consequences :
- Uncertainty regarding the security posture
- Risk of incidents or compromise
- Persistent cryptographic vulnerabilities
Non-compliance Risks
“ We are unable to demonstrate which cryptographic mechanisms we use, whether they are compliant, or how they are managed across the organization.”
Conséquences:
- Difficult decision-making at the executive level
- Uncoordinated decisions among teams
- Delays in establishing a PQC program
Lack of organization-wide control over cryptography
“ Without a comprehensive view of cryptography, it becomes impossible to manage risks and drive transformation.”
Consequences:
- Unidentified interdependencies between systems
- Risk of failures or disruptions during deployments
- Longer and more expensive migration projects
Inability to plan the transition to PQC
“ We don’t know where to start because we don’t know which systems need to be migrated to PQC.”
Consequences:
- Decision-making paralysis, a “wait-and-see” approach
- Roadmaps disconnected from operational realities
- Missed budget opportunities and transformation windows

“ANSSI advises public and private organizations to begin conducting an initial inventory now in order to gain a clear understanding of their use of cryptography.”
Our Approach
Take back control of your cryptography
CryptoNext COMPASS: an open solution designed to discover, inventory, and manage cryptographic assets within complex environments.
01
Get complete visibility
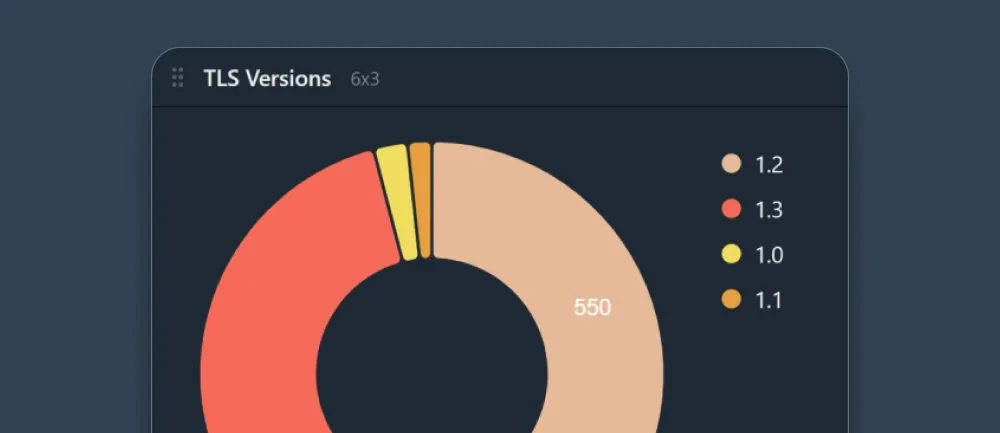
Map the use of cryptography across networks, protocols, and applications, including in IT and OT environments. CryptoNext COMPASS identifies cryptographic assets that are typically invisible or undocumented and presents them through clear, structured dashboards.
Quickly identify algorithms, certificates, keys, and dependencies to understand your risk exposure and effectively prioritize the migration roadmap to PQC.

02
Reduce risk
Quickly identify weak, obsolete, or non-compliant cryptographic algorithms, protocols, and certificates present within the data flows and infrastructure. Through its visualization dashboards, CryptoNext COMPASS highlights the actual use of encryption within your applications, networks, and systems.
Security teams immediately understand how cryptography is being used, detect risky mechanisms, and can take proactive steps to reduce vulnerabilities before they turn into incidents.

03
Strengthen governance and compliance
Generate a structured, centralized, and continuously updated cryptographic inventory designed to meet audit, regulatory, and long-term traceability requirements.
Using visual dashboards, CryptoNext COMPASS provides factual and actionable evidence of the true use of cryptography in your applications and infrastructure. Demonstrate compliance to risk teams, auditors, management, and authorities based on objective and verifiable data.

04
Prepare for the migration to PQC
You can’t migrate what you can’t see.
Identify exactly where your cryptographic assets are located to effectively prepare for the transition to post-quantum cryptography. CryptoNext COMPASS maps the algorithms, protocols, certificates, and dependencies present in your applications, networks, and infrastructure.
This visibility helps to prioritize your most critical assets, to assess the impact of changes, and to methodically plan the PQC roadmap, while securing every step of the migration.

Why CryptoNext Security?
Shed light on your cryptography
Unlock the hidden value of your data
Cryptographic data is scattered across silos. CryptoNext COMPASS aggregates and correlates it within a single platform, revealing hidden connections, underlying risks, and high-value insights to guide your PQC transition.
Build on an open platform
CryptoNext COMPASS integrates seamlessly into your ecosystem using customizable connectors. Integrate your existing tools, sensors, and systems to tailor the platform to your specific use cases and make COMPASS the central hub of your cryptographic governance.
Visualize end-to-end cryptographic dependencies
CryptoNext COMPASS maps the cryptographic dependencies between your applications and other components—such as networks, storage, protocols, and key providers. Visualize your entire cryptographic ecosystem and more easily identify risks, vulnerabilities, and compliance implications.
Manage regulatory compliance over the long term
CryptoNext COMPASS generates Cryptographic Bills of Materials (CBOMs) that align with the European Commission’s requirements, which call for a comprehensive inventory by the end of 2026. Asset traceability, customized reporting, and continuous auditing turn compliance into an operational advantage.

Resources